Your Security Defenses Are Missing Threats.
We Find the Gaps and Close Them.
Proactively simulate attackers, find detection gaps, and deploy improvements. Agentic AI powered CTEM.
Isolated environment. No risk to production. Results the same day.
The Difference is Clear
Most tools stop at "you have a gap." RefineSec finds the gap and delivers ready-to-deploy rules that close it. Comparison below: manual pen testing, traditional BAS, RefineSec.
We run each attack until your defenses miss it, then deliver rules for that variant.
| Manual Pen Testing | Traditional BAS | RefineSec (Agentic AI) | |
|---|---|---|---|
| Real Adversary Techniques | Partial | ||
| Polymorphic / mutated execution (bypass & evasion) | |||
| Multi-Control Testing (EDR, XDR, AV, DLP, more coming) | Limited | ||
| Autonomous Execution | Partial | ||
| MITRE ATT&CK Mapping | Partial | ||
| Ready-to-Deploy Detection Rules | |||
| Solution-oriented (delivers detection rules) | Partial | ||
| Context-Aware Remediation | |||
| Continuous Validation | |||
| Deploy & Run in Under 1 Hour | |||
| Board-Ready ROI Reporting | Limited | ||
| Agentic AI Engine |
Continuous Threat Exposure Management Powered by Agentic AI
RefineSec runs the full CTEM cycle: research threats, simulate adversary techniques, validate defenses, generate detection improvements. Endpoint first; architecture expands to firewall, SIEM, cloud.
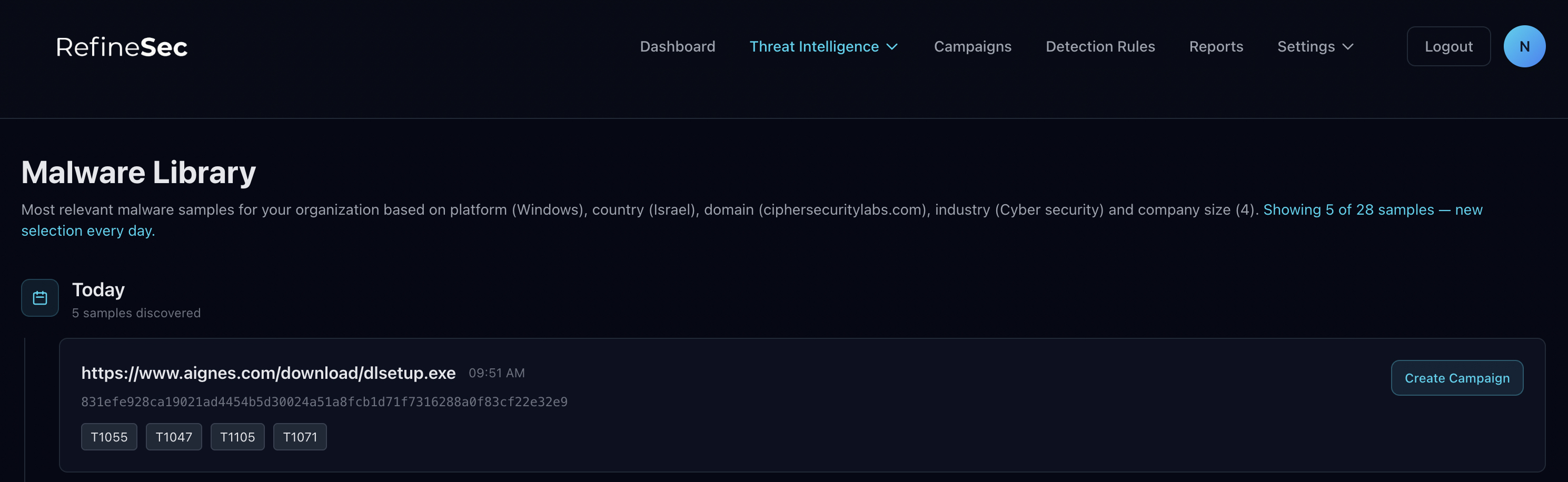
Agentic AI collects intelligence, studies attacker TTPs and malware, and turns research into ready-to-deploy detection rules.
Click a step above to read more.
Find Gaps. Deploy Rules. Strengthen Posture.
Three steps: deploy in isolation, simulate real threats, close gaps with detection rules. No risk to production. Same-day results.
Deploy in Minutes
Isolated. Zero risk to production.
Lightweight agent on one VM alongside your tools. No network or integration changes. First campaign in under an hour. Endpoint first; more controls coming.
Simulate Real Threats Autonomously
Agentic AI researches threats, models TTPs, then simulates against your defenses in multiple variants until bypass. Pick threat actors (LockBit, BlackCat, TA505) or techniques. We run until something slips through, then generate rules for it.
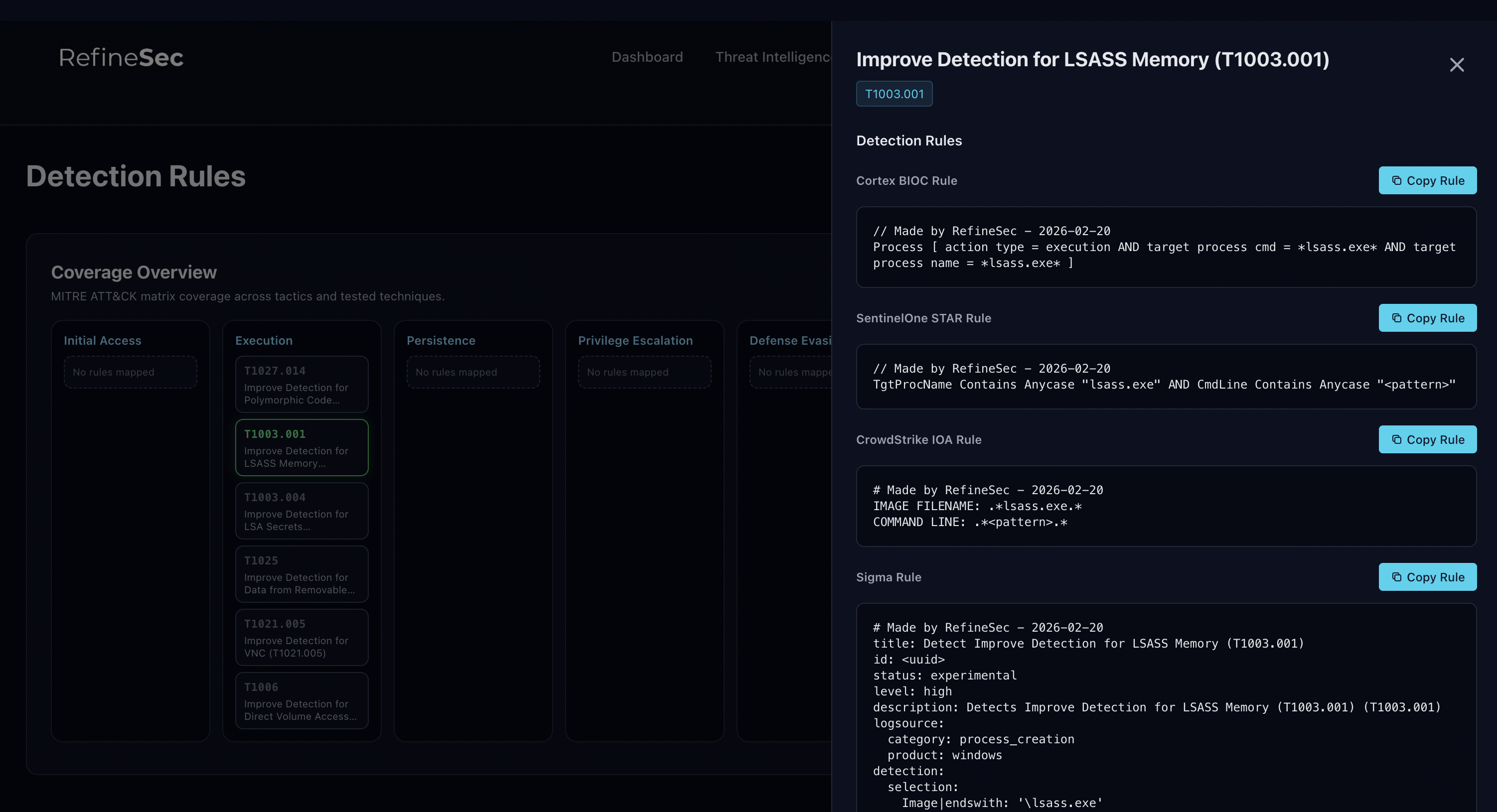
Close Gaps with Detection Rules
Solution-driven: every finding comes with deployable rules. Coverage scores, multi-vendor comparison, ready-to-deploy rules per gap. Deploy the fix today.
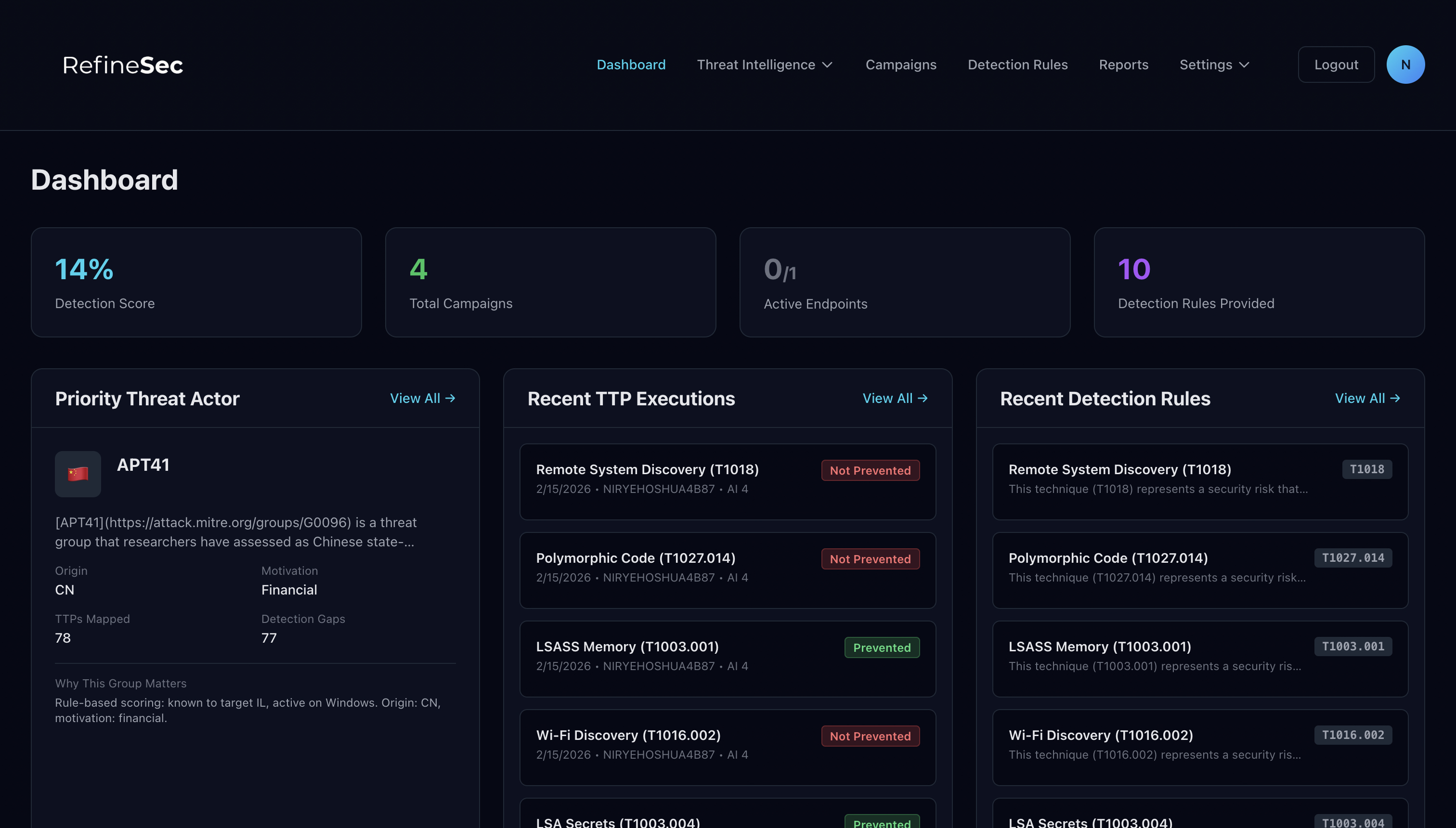
One Dashboard. Complete Clarity.
Every attack, every detection, every gap. Compare tools side by side. Endpoint today; firewall, SIEM, cloud coming.
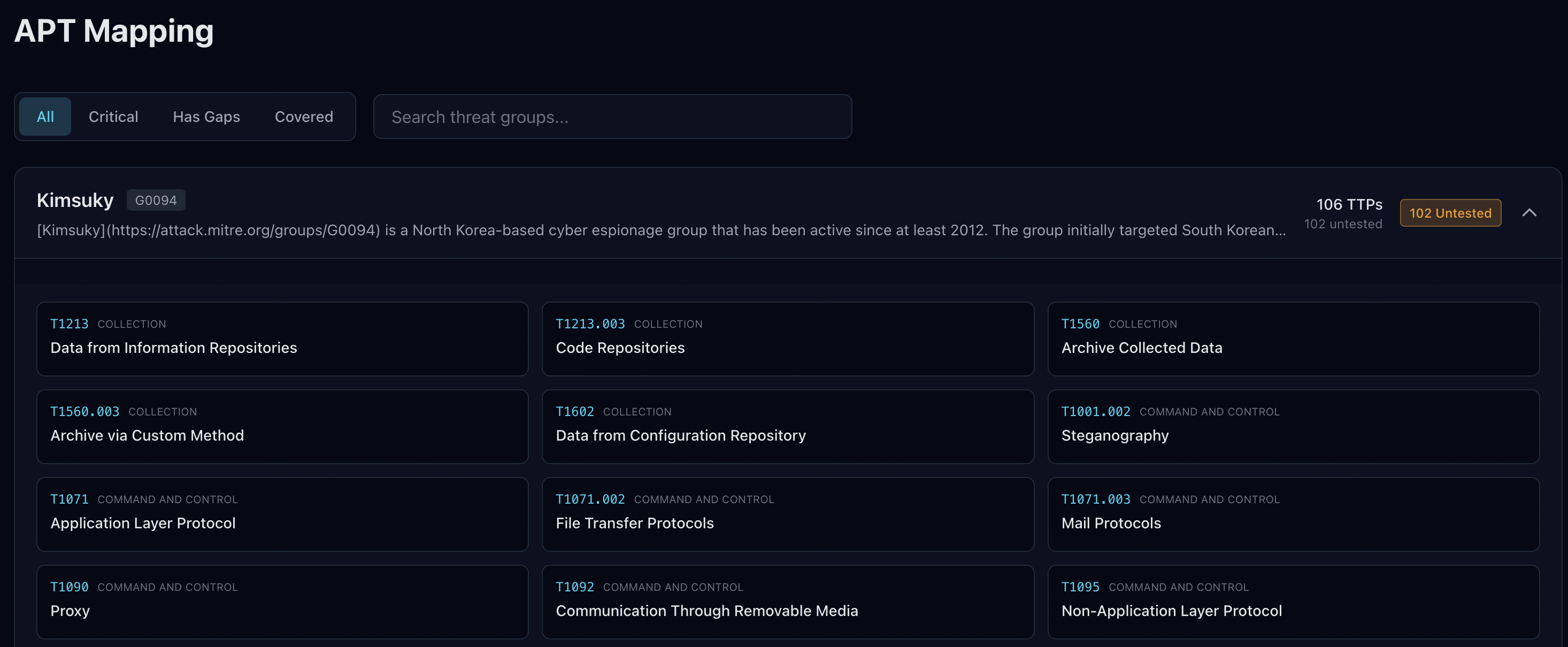
Test Against the Threats That Matter
Pick attackers and techniques relevant to your industry. Real breach methods. We run each attack in many ways until your defenses miss it, then deliver rules for those variants. All techniques MITRE ATT&CK mapped. Platform runs tests, collects tool output, and analyzes gaps autonomously.
Numbers Your Board Will Understand
Detection data turned into board-ready ROI insights.
Know Your Coverage Score
Coverage like "73% against LockBit, 41% against BlackCat." Scores by adversary, technique, and vendor. Decide on data, not vendor claims.
Don't Just Find Gaps. Close Them.
Every finding comes with rules you can deploy immediately.
Detection Rules That Write Themselves
For every missed technique: ready-to-deploy rules (Sigma, YARA, vendor-native). Deploy and close the gap. Endpoint first; more control types coming. MITRE-mapped, impact-prioritized, environment-tailored. Stronger posture with every campaign.
Built for Every Role on Your Security Team
Insights for every role, from board to SOC.
Gaps closed, not just found. Data-backed answer to "Are we protected?" and ROI you can show the board.
See which controls perform best against which threats. Stack decisions from real data, not vendor claims.
See why an attack was missed and which variants slipped through. Get rules that catch those variants in your tool formats.
We run attacks until one gets through, then deliver rules for it. Before/after metrics and rules for every variant that slipped through.
Works with the platforms you trust
Test controls against real techniques. Get rules in your tool formats. Endpoint first; SIEM, firewall, cloud coming.
EDR & XDR








SIEM & Log Aggregation










Align with the frameworks that matter
Validation and detection aligned to your standards. Map coverage, prove control effectiveness, close gaps with audit-ready evidence.
NIST Cybersecurity Framework
Validate detection coverage against Identify, Protect, Detect, Respond. Adversary-based testing and ready-to-deploy rules for evidence.
ISO/IEC 27001
Evidence for operations security (A.12) and related annex controls. Detection effectiveness across controls to support ISMS and audits.
PCI DSS
Evidence for Req 11 (testing) and Req 10 (logging and monitoring). Regular testing and detection coverage for assessors.
NIS2 Directive
Detection and response for essential and important entities. Autonomous testing and detection rules for resilience evidence.
DORA
ICT risk and detection evidence for resilience testing. Financial entities prove detection and response effectiveness.
MITRE ATT&CK
Every technique mapped to ATT&CK. Coverage by tactic and technique, rules linked to IDs, clear view of stack vs real adversary behavior.
CIS Controls
Map validation and detection to CIS Controls. Evidence tied to control IDs and real-world technique coverage.
SOC 2
Evidence for Trust Services Criteria (security, availability, confidentiality). Demonstrate operational effectiveness for auditors.
NIST 800-53
Map coverage to SP 800-53 controls. Evidence for control families (e.g. IR, SI, RA) via adversary testing and detection rules.
Built on 20+ years of offensive and defensive security research
Authors of best-seling books"Antivirus Bypass Techniques" and "MAoS - Malware Analysis on Steroids"
See What Your Defenses Are Missing
Run your first campaign in under an hour. Get real detection coverage scores, find out exactly where your gaps are, and walk away with deployable rules that close them. No long onboarding. No risk to production. Just results.
Request Demo

